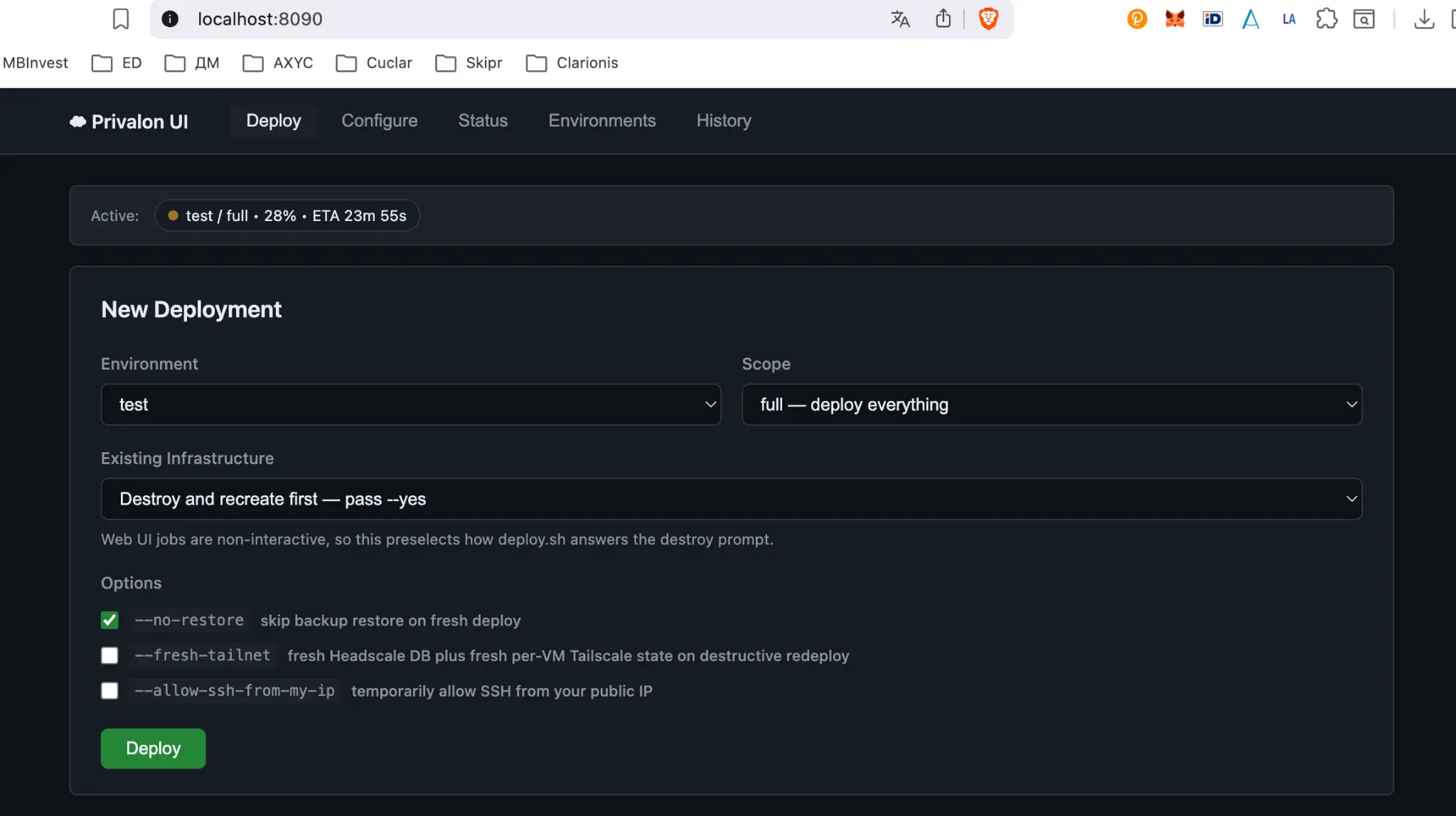
Deploy from your browser.
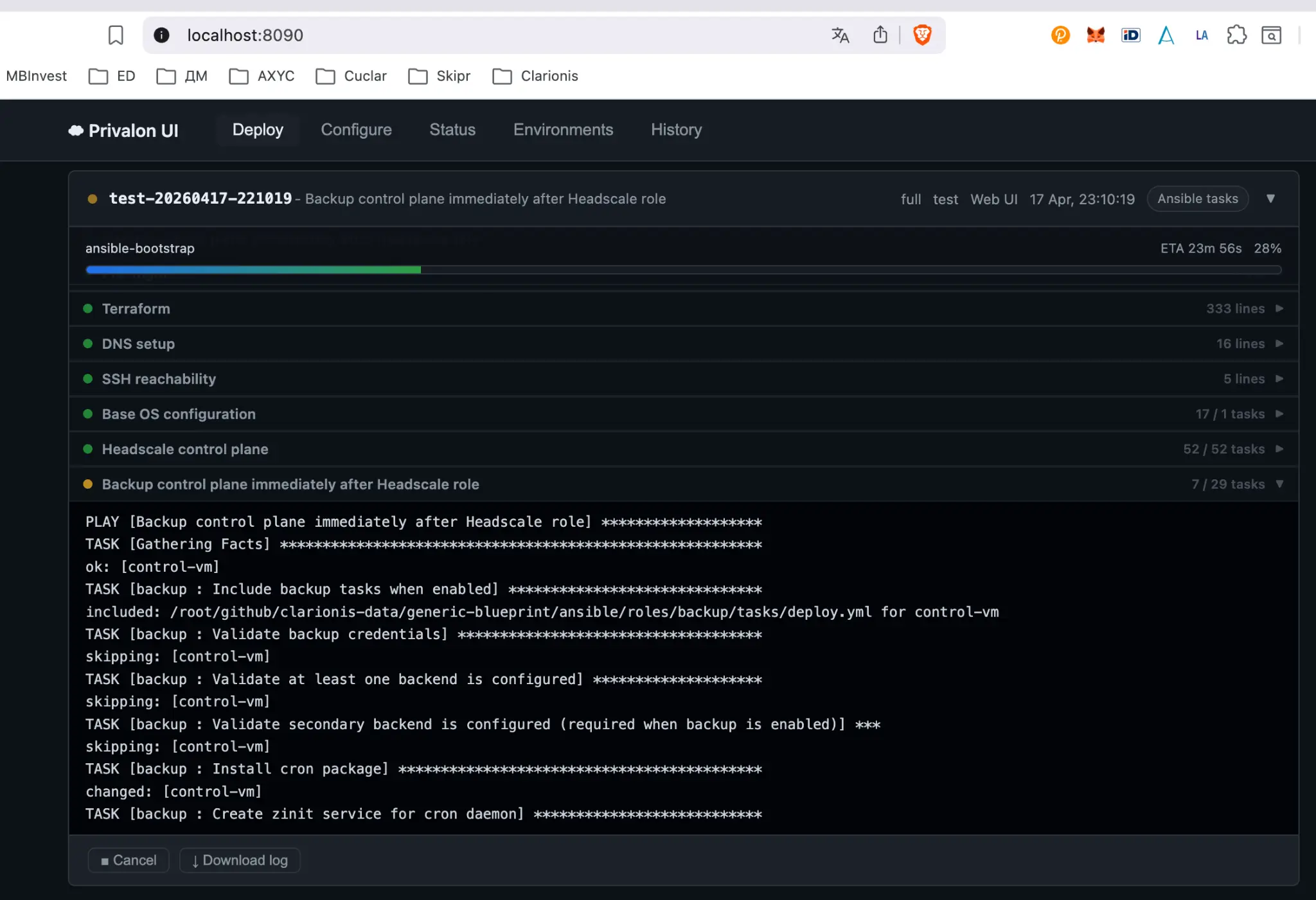
Logs stream live.
Privalon ships with a locally-hosted Web UI that wraps the deploy scripts. Select environment, scope, and options — then watch Ansible tasks execute in real time. Never exposed to the internet.